What makes an effective disaster recovery plan?

At a glance
- With IT recovery protocols in place, a company can maintain business operations during and after disruptive events.
- The goal of a contingency plan is to keep all systems operational during a disaster. A disaster recovery plan, however, focuses on returning IT operations, and everything they affect, back to normal after a disruption.
- An effective disaster recovery plan includes creating network maps, backups and policies for rapid recovery of systems and data loss.
- Want to build your IT skills? Learn more about online IT programs at University of Phoenix.
What is a disaster recovery plan?
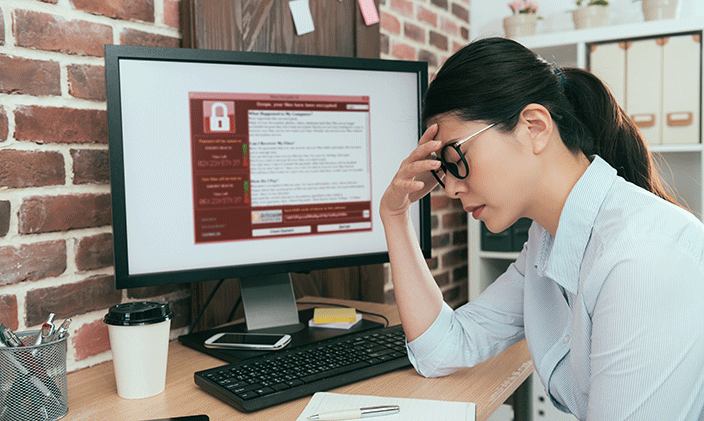
From cyberattacks to crashing servers to extended power outages, technology has vulnerabilities that can have far-reaching effects. This is especially true for businesses. Organizations that rely on technology not only have to work to mitigate risk for such disruptions, but they also need a plan of action for if and when such interruptions occur. This plan is often called a disaster recovery plan, and it offers step-by-step instructions for protecting and recovering vital systems and data.
What is the importance of a disaster recovery plan?
Unplanned downtime can significantly impact business operations, not to mention an organization’s bottom line. A study by Deloitte, one of the world’s largest accounting firms, revealed that some companies that experienced a cyberattack saw, on average, a full-level downgrade in their credit rating.
Getting ahead of disasters like cyberattacks — as well as recovering quickly when one occurs — is the primary goal of a disaster recovery plan. The importance of a disaster recovery plan cannot be understated. With recovery protocols in place, your business can:
- Maintain mission-critical continuity during and after disruptive situations
- Provide superior customer-service experiences
- Prepare cybersecurity professionals to react quickly to hardware, software and network failures
- Minimize the impact of interruptions on operations
- Reduce the economic impact of the interruption on your business’s financial health
- Establish and test alternative ways to conduct business during a crisis
- Train employees on emergency procedures, empowering them to keep calm during tense times
- Create a plan for quick and efficient service restoration
How does a disaster recovery plan differ from a contingency plan?
Many businesses debate which is more important — a contingency plan or a disaster recovery plan. The truth is both are necessary for an overall business continuity plan.
Both involve proactive strategies that reduce negative impact of a disaster before, during and after one happens. Both are crucial for businesses that must survive during inclement weather, pandemics and cybersecurity threats. The differences, however, are key.
While similar, business continuity and disaster recovery plans serve different purposes. In short, the goal of a contingency plan is to keep everything running during a disaster. A disaster recovery plan, however, works to get operations back to normal after one occurs.
Contingency plans guide overall operations, while a disaster recovery plan focuses on IT-related issues, like recovering data and restoring critical systems after cyberattacks. In addition, while contingency plans help reduce downtime across the entire company, disaster recovery plans primarily focus on the functionality of IT systems.
Do I need a contingency plan and a disaster recovery plan?
Many companies include a disaster recovery plan within their overall contingency plan. The two plans complement each other. A business needs a contingency plan to remain operational when issues arise and a disaster recovery plan to implement the crucial IT elements of that plan.
Who needs a disaster recovery plan?
Any company that uses computers or relies on technology needs a disaster recovery plan. A breakdown in business operations can result in unexpected costs, lost revenue, unhappy customers and a tarnished reputation. The longer it takes to recover, the bigger the impact on operations. With a disaster recovery plan, your business can bounce back more quickly from a crisis, regardless of where, how or when one occurs. Any company focused on prevention that sees the value in getting ahead of disasters needs to develop a disaster recovery plan.
What should a disaster recovery plan include?
An effective disaster recovery plan depends on your business’s size, scope and operations. The specific procedures and measures will depend on your business needs and long-term goals but generally should include the following:
- Appointing on-site employees to specific roles and responsibilities during a crisis to establish redundancies and reduce errors
- Ensuring contingencies when responsible individuals are unavailable
- Updating your IT and application inventory regularly, including hardware, software and cloud-based services
- Creating network maps, backups and policies for rapid recovery of systems and data loss
- Detailing how, when and where all IT resources are backed up
- Documenting all emergency-response procedures for any situation, such as fire, natural disasters and cyber threats
- Listing step-by-step backup operations procedures to keep essential data processing and IT tasks running
- Outlining recovery actions to initiate rapid systems restoration
- Testing the disaster recovery plan regularly and practicing dry runs with employees to ensure they understand their responsibilities
- Holding debriefings after recovery from a disruption and documenting what was learned
read similar articles

How to get into cybersecurity: Degrees, careers and salaries
How to develop an effective disaster recovery plan
All companies can develop — and benefit from — a disaster recovery plan. It boils down to a simple cost–benefit analysis: Recover quickly and gain a competitive edge or recover slowly and lose customers and sales.
Developing an effective disaster recovery plan begins with analyzing security risks, so impact analysis and risk assessment skills are needed to understand and predict potential hazards. Be sure to look beyond IT. Consider infrastructure and geographical risk factors, as well as the critical technology needs of each department.
From there, following the bullet points listed above will provide a good start to a disaster recovery plan tailored to your organization.
Who is responsible for developing a business’s disaster recovery plan?
There should be responsible primary point of contact who can develop, deploy and manage a disaster recovery plan.
Some companies, especially smaller businesses, hire contractors or consultants to develop and implement disaster recovery plans. Others have an in-house information manager who is in charge during a crisis. Either way, you’ll want skilled professionals who have experience in technology and education in computer information systems to lead your company out of whatever storm occurs and into a safe harbor of restored data and operations.

Information technology program options at University of Phoenix
Whether you’re seeking to gain a basic understanding of information technology or cybersecurity, or you’re a working professional looking to expand your skills, University of Phoenix offers online course collections, bachelor’s degrees and master’s degrees. These include:
- Bachelor of Science in Information Technology — In this program you’ll learn essential cyber skills including business process, cybersecurity, information systems, operations and systems analysis.
- Bachelor of Science in Cybersecurity — This online program teaches skills such as security policies, network security, cybersecurity and more.
- Master of Science in Cybersecurity — This online program explores in depth such skills and topics as cybersecurity, security policies and vulnerability.
- Certified Ethical Hacker Course Collection — This course collection can help you prepare for the EC-Council Certified Ethical Hacker (CEH) certification exam. Topics include the phases of ethical hacking, recognizing weaknesses and vulnerabilities of a system, social engineering, IoT threats, risk mitigation and more.
- Certified Incident Handler Course Collection — This course collection can help you prepare for the EC-Council Certified Incident Handler (ECIH) certification exam. This specialist certification focuses on how to effectively handle security breaches.
- Certified Network Defender Course Collection — This course collection can help prepare you for the entry-level EC-Council Certified Network Defender (CND) certification exam. Courses focus on protecting a network from potential security breaches.
- Computer Hacking Forensics Investigator Course Collection — This course collection can help prepare you to sit for the EC-Council Computer Hacking Forensics Investigator (CHFI) certification exam. You’ll learn about the latest technologies, tools and methodologies in digital forensics, including the dark web, IoT, malware, the cloud and data forensics.
want to read more like this?